Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT network. Security Operations Centers (SOC) rely on logs and events generated by industrial assets — PLCs, HMIs, historians, engineering workstations and OT network infrastructure — to detect anomalies and investigate incidents. In most organizations, these events are forwarded to an enterprise SIEM platform where the SOC performs monitoring and correlation.
However, when industrial environments are protected by hardware data diodes or unidirectional gateways, enabling this visibility becomes significantly more complex. Forwarding logs across a strictly one-way boundary introduces architectural challenges that traditional IT monitoring solutions were not designed to address.
Based on Cyberium’s experience deploying data diodes in critical infrastructure environments, several architectural patterns have emerged — each offering different trade-offs between visibility, reliability and security.
Why OT telemetry MUST reach the SOC?
Without centralized visibility, security teams effectively operate blind. Suspicious authentication attempts, abnormal control commands or unexpected configuration changes may occur inside the OT environment without being detected until operational impact becomes visible. In industrial environments where safety and availability are critical, delayed detection can translate directly into operational disruption.
Real-world incidents illustrate this challenge. During the cyberattacks against the Ukrainian power grid in 2015 and 2016, attackers were able to manipulate industrial control systems and open circuit breakers across multiple substations, cutting power to hundreds of thousands of customers. Post-incident analysis showed that attackers moved through several stages of intrusion before triggering the outage.
Centralizing OT security telemetry within the SOC enables analysts to correlate events across IT and OT environments, detect anomalies earlier and investigate incidents using a unified monitoring platform. Industrial cybersecurity standards such as IEC 62443 and NIST SP 800-82 highlight centralized monitoring as a key element of defense-in-depth strategies, improving cross-domain correlation and reducing response time when anomalies occur in industrial environments.
Why OT security visibility is difficult in one-way architectures?
Data diodes are increasingly deployed to enforce strict separation between OT and IT networks. By enforcing one-way communication, they prevent any inbound cyber access to industrial control systems. While this model significantly improves security, it also introduces architectural constraints when integrating OT monitoring into existing SOC infrastructures.
Protocol limitations in one-way architectures – Many log forwarding mechanisms rely on bidirectional communication (TCP acknowledgments, API sessions, TLS handshakes), which are incompatible with strictly unidirectional data flows enforced by data diodes.
Log normalization constraints – OT devices often produce incomplete or proprietary logs that require enrichment before SIEM ingestion. In one-way architectures, the absence of bidirectional communication limits traditional normalization and lookup mechanisms.
Reliability risks in telemetry transmission – Some diode-based implementations rely on UDP forwarding, which may introduce packet loss and create security visibility gaps if critical events are dropped during transmission.
Options for forwarding OT logs to the SOC
Two main architectural approaches are typically used to forward OT security telemetry to a SOC through a unidirectional gateway.
ARCHITECTURE #A
The first approach places the data diode directly between OT assets and the SIEM infrastructure, allowing devices to forward their logs across the one-way boundary. Since most diodes support UDP forwarding, syslog messages can be transmitted relatively easily. This architecture is simple and quick to deploy and generally requires minimal changes to the OT environment. However, it introduces several limitations. Packet loss may occur depending on the implementation, source IP information may be altered during transmission, and the absence of an intermediate collector makes log normalization or enrichment more difficult.
ARCHITECTURE #B
A more advanced approach places the diode further upstream, between the OT log collector and the SIEM indexer. In this model, logs are first aggregated, normalized and enriched within the OT environment before being transmitted toward the SOC. This significantly improves data quality and increases the effectiveness of SOC monitoring and correlation. The main challenge lies in the forwarding mechanisms themselves, as many SIEM collectors rely on TLS handshakes or certificate exchanges with the indexer — interactions that are incompatible with strictly unidirectional communication models.
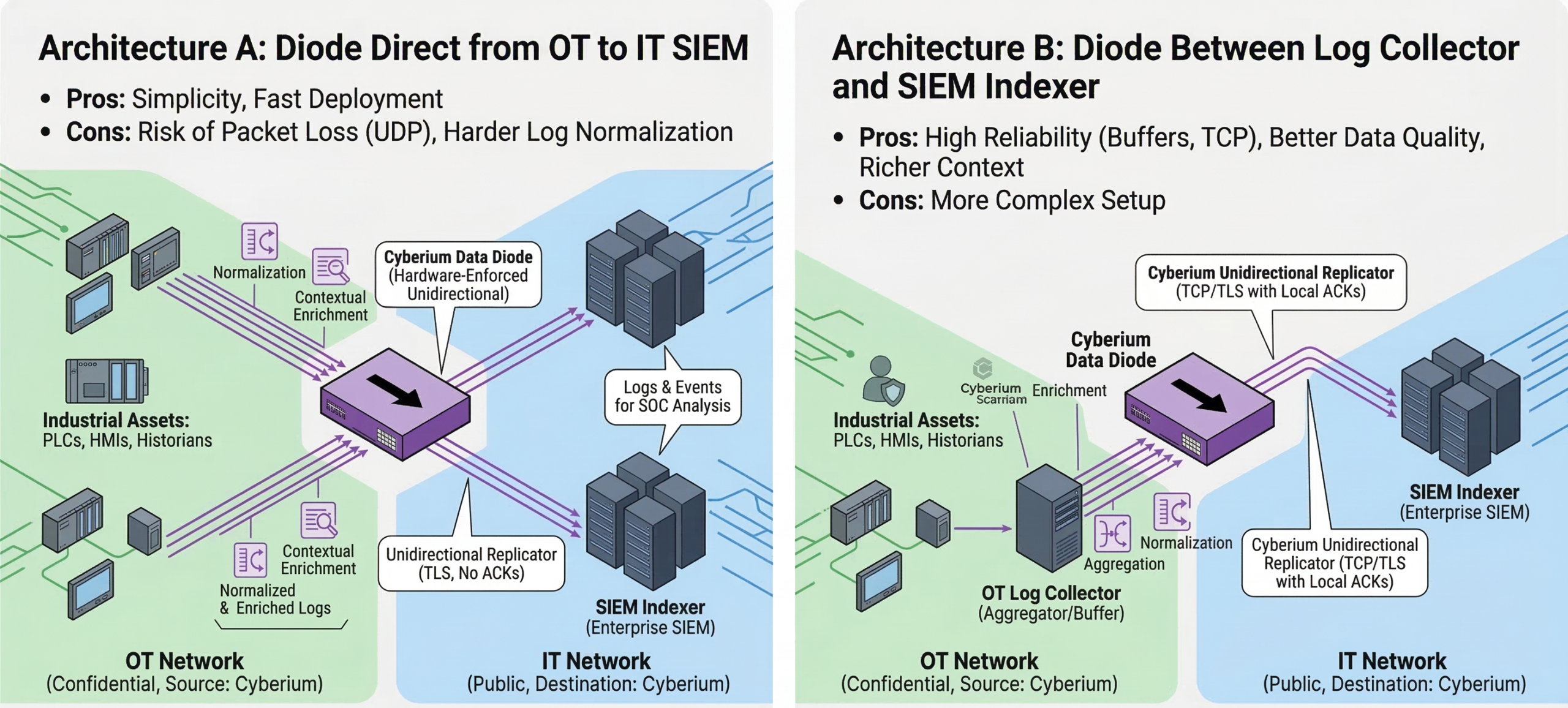
To address this constraint, specialized replication mechanisms are required. Cyberium’s architecture, for example, integrates with SIEM platforms such as Splunk through secure replication connectors designed specifically for unidirectional environments.
Conclusion
Achieving visibility across OT networks remains one of the most fundamental challenges in industrial cybersecurity. While strict network segmentation is essential for protecting industrial systems, it should not come at the expense of security monitoring.
With the right architecture, organizations can forward OT security telemetry toward their SOC while maintaining the integrity of the one-way security boundary. Hardware-enforced data diodes combined with appropriate log forwarding mechanisms make it possible to preserve both strong isolation and full operational visibility — two requirements that modern critical infrastructure operators can no longer afford to treat separately.




