Unidirectional Cross-Domain Data Transfer
Enabling sovereign cross-domain data exchange for defense and national security missions,
combining operational agility with uncompromised classified isolation.
Protecting Sovereign Missions in an Era of Escalating Threats
Government and defense organisations operate under unique cyber pressures: they must enable secure information sharing across classification boundaries while safeguarding national security, critical decision systems, and mission effectiveness. At the same time, adversaries are increasingly resourceful, state-sponsored, and focused on undermining sovereign operations — not just data theft.
In this context, traditional detection-first cybersecurity approaches can no longer deliver the necessary assurance. Structural protection, information assurance, and rigorous domain separation are now strategic imperatives.
Key Cross-Domain Security Challenges to Overcome
Threat Landscape for Gov & Defense — In Numbers
Cross-domain exposure and sovereign information risk are rising alongside increasingly sophisticated state-linked campaigns and national-level cyber incidents.
Increase in ransomware attacks targeting government agencies in 2024 compared to 2023, underscoring growing assaults on public sector infrastructure
Substantially rising average of nationally significant cyber incidents reported by UK’s National Cyber Security Centre, with “highly significant”
…of observed 2024 attacks were aimed at government agencies, highlighting sustained targeting of public-sector environments
Why Cyberium’s Solution is a Natural Fit for Government & Defense Environments?
Hardware-Enforced Cross-Domain Isolation for Classified Environments
Physical domain separation aligned with national and international security accreditation frameworks
In government and defense environments, adversaries are often state-sponsored actors seeking intelligence compromise, persistence, or strategic disruption. Software-based segmentation mechanisms — even when hardened — remain dependent on configuration integrity, patch cycles, and rule management, which complicate accreditation and long-term assurance.
Cyberium enforces physical, hardware-level unidirectional isolation between security domains, ensuring that no return path exists by design. This structural enforcement simplifies accreditation processes and provides deterministic protection suitable for sensitive, classified, and sovereign environments.
Mission-Critical Cross-Domain Data Transfer — Without Policy Complexity
Operational data sharing that preserves strict domain control
Defense and government missions require secure movement of intelligence, telemetry, situational awareness data or logs between classification levels — without creating reverse paths or uncontrolled trust relationships.
Cyberium combines hardware-enforced one-way communication with modular proxy software to enable structured, protocol-aware data transfer across domains. Cross-domain exchange is achieved without broker-to-broker sessions, reverse sessions or complex rule maintenance — preserving strict domain separation while enabling operational continuity.
Sovereign Architecture & High-Assurance Trust Model
Technology control, supply-chain confidence and formal assurance
In sovereign environments, trust extends beyond cybersecurity posture to the origin, evaluation and governance of security components. Dependence on opaque or non-sovereign supply chains introduces strategic risk.
Cyberium’s architecture integrates European-origin optical enforcement technologies and formally evaluated components, enabling sovereign control over the most critical security boundary. Combined with patented active-active resilience and high-availability design, the platform ensures continuous operation even in degraded conditions — without weakening domain isolation.
Certification Frameworks


Domain-Specific Segmentation Applications
Multiple applications, one shared Cross-Domain reality: secure, high-performance data exchange under strict sovereign compliance.
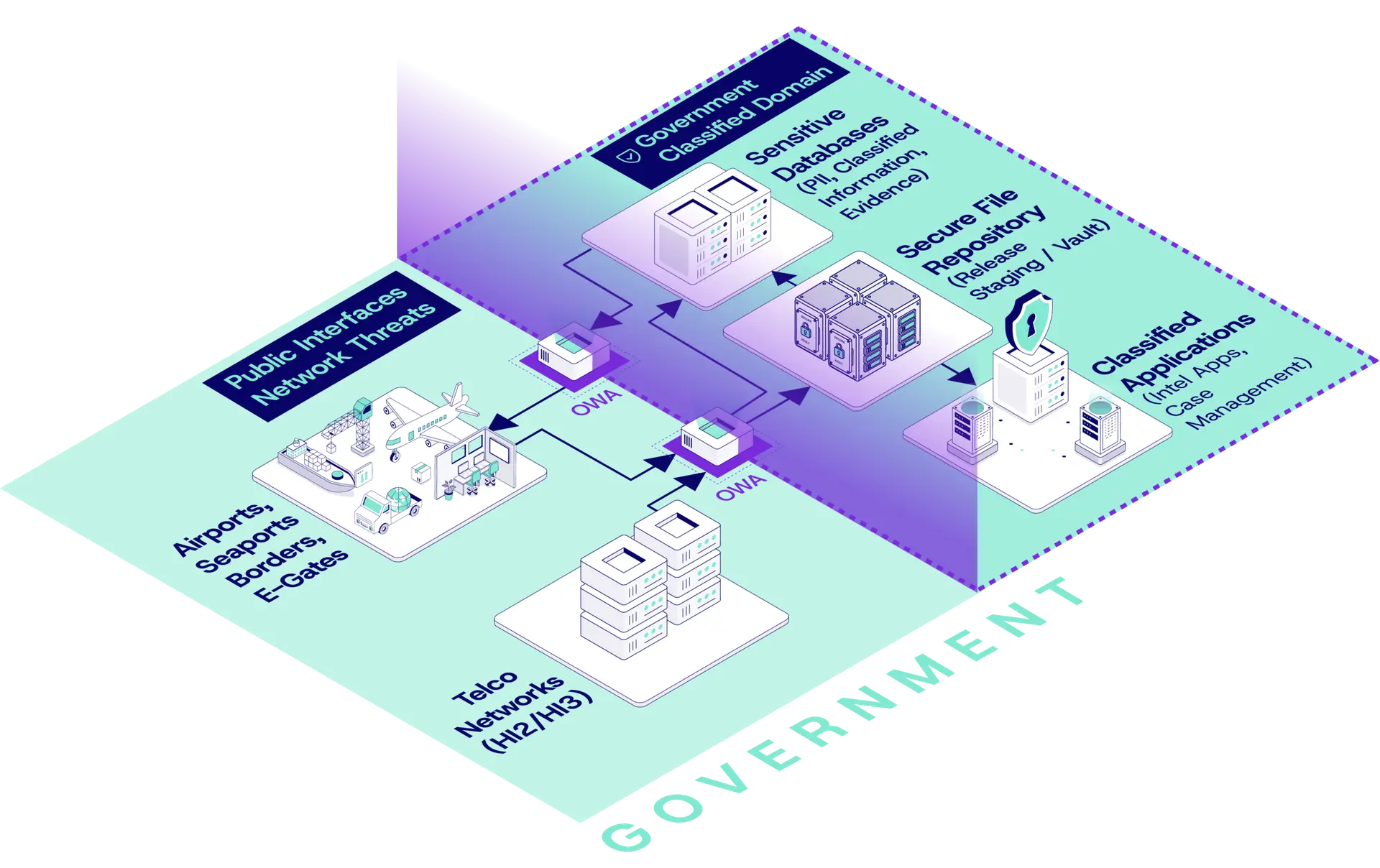
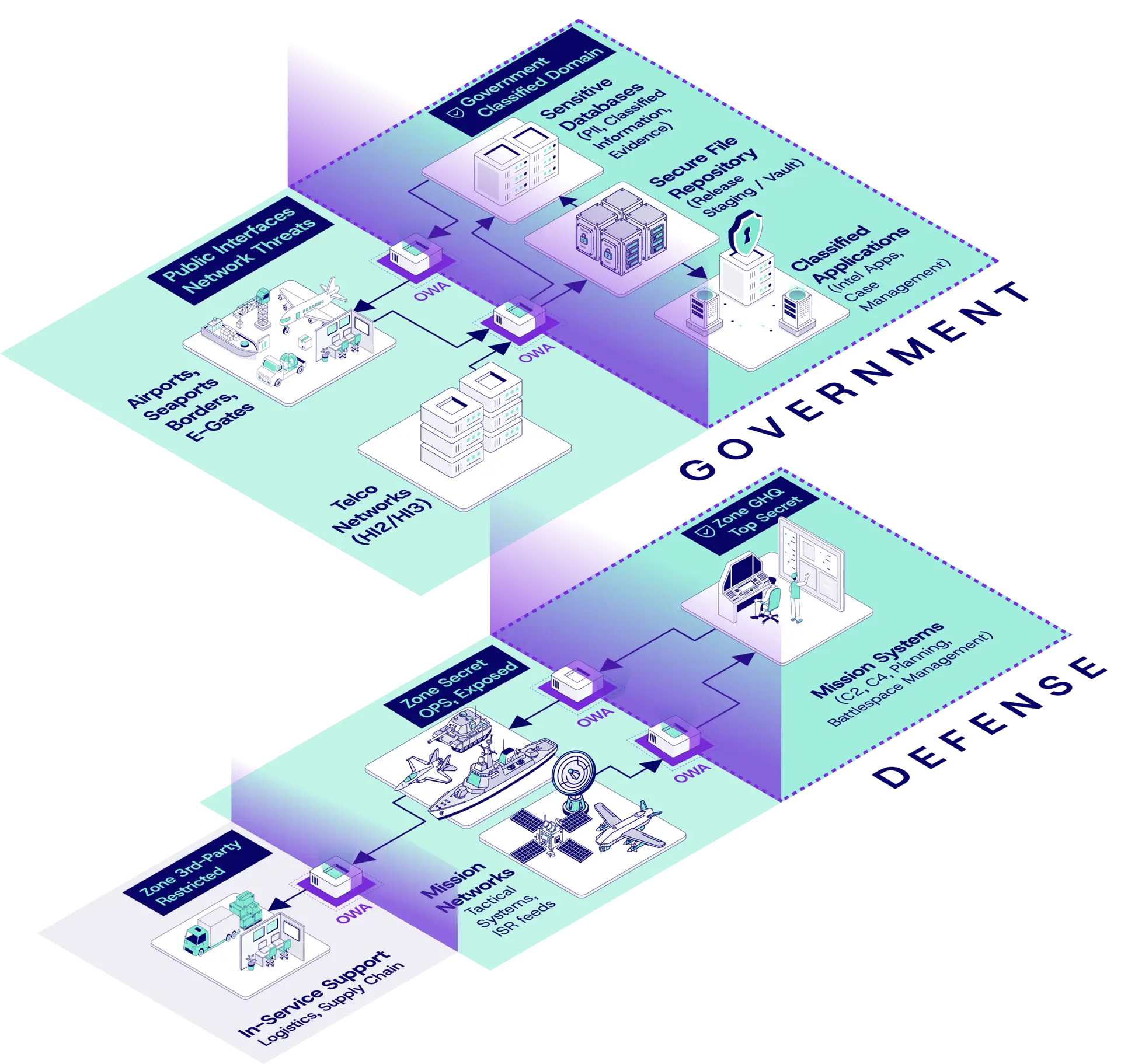
Homeland Security & MoI — Border & Civil Protection
National border control, immigration, lawful interception and internal security infrastructures operate across mixed exposure levels — from Internet-facing eGate systems to classified intelligence databases. Operational efficiency requires near real-time data availability, yet these environments are prime targets for state-sponsored actors and data exfiltration campaigns.
The structural challenge lies in enabling controlled data dissemination (watchlists, passenger records, investigative feeds) without introducing any inbound path into classified domains. Accreditation bodies require demonstrable domain separation, deterministic data transfer and strict compliance with national sovereign security frameworks.
Secure export of watchlists to airport eGate systems.
Controlled sharing of immigration or biometric databases toward operational networks.
Segmentation between public-facing services and Restricted national databases.

National Intelligence & Classified Systems
Intelligence agencies must exchange high-value data across multiple classification levels while preserving strict separation between Secret, Top Secret and Restricted domains. Unlike enterprise IT, these systems cannot rely solely on monitoring and remediation — architectural prevention is mandatory.
Cross-domain mechanisms must guarantee deterministic transfer, no data loss, and absolute non-reversibility, even under adversarial conditions. Additionally, these environments demand formally evaluated security components and auditable compliance under national and NATO-aligned frameworks.
High-volume ingestion of lawful interception and investigative data (HI2/HI3) into classified monitoring environments
Controlled dissemination of classified intelligence datasets to operational networks
Secure synchronization of classified databases without bidirectional replication
High-volume encrypted file transfer across classification boundaries

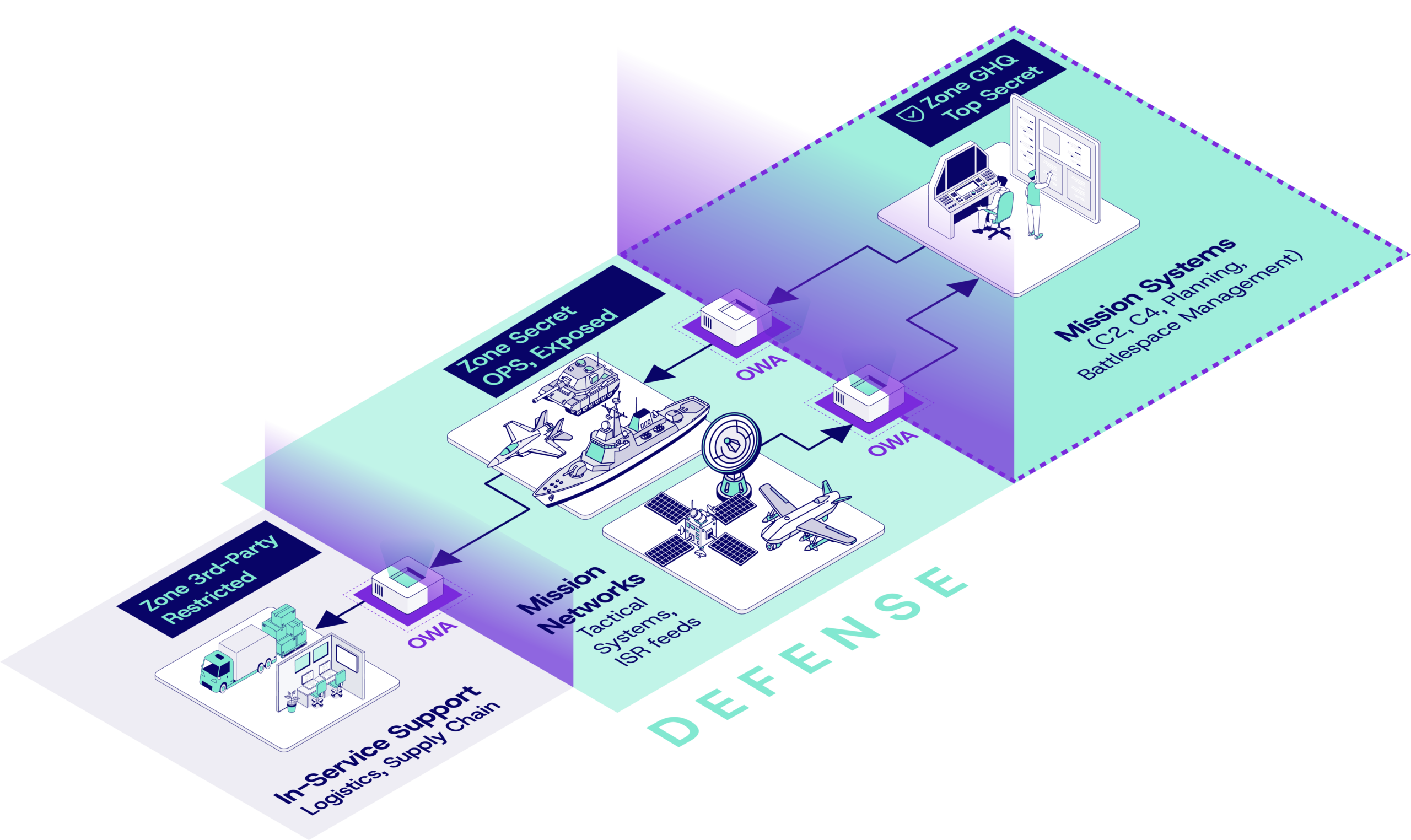
Defense & Mission Systems
Modern defense environments combine legacy tactical platforms with network-centric architectures (C4ISR, ISR feeds, radar, UAV, naval systems). Mission data must circulate at high speed across security domains — often between coalition and sovereign networks — without risking compromise of core systems.
Operational theaters impose harsh conditions: remote deployment, minimal maintenance windows, and strict availability requirements. Cross-domain systems must therefore combine hardware-enforced one-way security with very high throughput, zero data corruption and autonomous resilience.
Coalition air picture sharing between national and joint command networks.
Isolation of C4ISR cores while enabling outbound data dissemination
Segmentation of mission systems from logistics or contractor networks
High-reliability real-time UDP-based tactical feeds across classification levels

Secure OEM, Logistics & Sustainment Ecosystems
Defense programs increasingly require secure data exchange between sovereign military systems and external contractors, OEMs or sustainment partners. While maintenance, logistics and lifecycle management depend on connectivity, operational networks cannot tolerate inbound risk from third parties.
The challenge is to enable high-volume file exchange, patch distribution or telemetry export across organizational boundaries while maintaining strict separation and sovereign control.
Secure in-service support data transfer from mission networks to contractors
Controlled patch and update delivery into restricted defense environments
One-way export of aircraft maintenance data to OEMs.
Segmentation between operational systems and supply-chain networks

Trusted by Military & Governmental entities
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES, SQL Databases Agent
- Gov & Defense
- OWA 2U/3U
- Bitdefender, ClamAV
- SFTP, FTP/S/ES
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES
Key Benefits. With Cyberium, Gone are the Days of...
Zero-day Anxiety
Eliminated by removing inbound attack paths
Complex Cross-Domain Architectures
Simplified through hardware-enforced domain separation
Enforce a sovereign-grade security boundary at the perimeter, reducing internal compensating controls while enabling high-performance cross-domain exchange.
Operational Fragility
Replaced by deterministic, high-availability performance
Supply-Chain Uncertainty
Addressed through sovereign-grade security components
Protected by our Cross-Domain solution for Gov & Defense







We secure the Sovereign
— connecting what should stay isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)




