
- Gov & Defense
- Bitdefender, ClamAV
Case Study: Lawful Interception with Zero Data Loss
Law Enforcement Agency - Undisclosed location
Extremely high malware exposure due to external interception sources
Zero tolerance for data loss — intercepted data cannot be retransmitted
Sustained 10 Gbps throughput with thousands of small files per second and occasional large payloads
Strict isolation requirements between public and classified environments
Need / Problem / Context
Secure Ingestion of Lawful Interception Data into Classified Environments
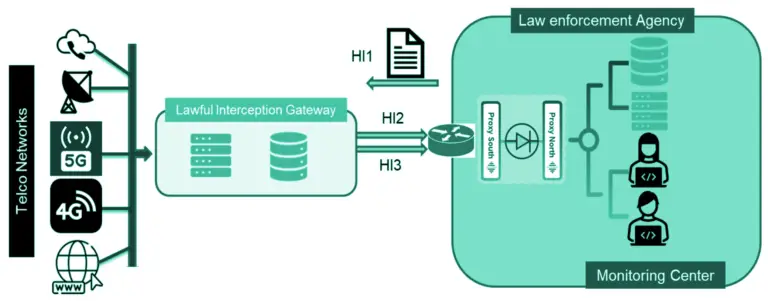
A national law enforcement agency needed to receive near real-time lawful interception traffic over HI2 and HI3 interfaces into a classified (“Secret”) network. This data, originating from telecom operators and external interception points, had to be continuously ingested and made available for analysis within a highly secure environment. The challenge was to ensure seamless, high-throughput data transfer while strictly preventing any risk of data leakage or backflow from the classified network, in compliance with stringent internal security and regulatory requirements.
Solution deployed
To meet both performance and security constraints, Cyberium deployed a high-throughput unidirectional architecture combining hardware isolation with application-layer controls and buffering mechanisms.

OWA 3U pack @ 10 Gbps
High-performance data diode ensuring strict one-way transfer from public to classified network.

Standard Connector (SFTP)
Standard connector enabling structured and controlled file ingestion across domains

Dual-engine Antivirus Scanning
Inline inspection of incoming data to mitigate malware risks before entering the secure network.


10 TB Buffering System
Absorbs burst traffic and guarantees reliable delivery without packet or file loss.
How It Works — Architecture Overview
Outcomes & benefits
The new architecture significantly improved both operational efficiency and infrastructure footprint while strengthening security guarantees.
Replaced 8× legacy 1 Gbps data diodes with a single 10 Gbps system, at a fraction of the cost
Reduced file transfer latency from days to seconds, with zero data loss and 99.99% availability
Freed 13U of datacenter space, reducing power and cooling requirements
More use cases
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES, SQL Databases Agent
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES
We secure the Sovereign
— connecting what should stay isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)




