
- Gov & Defense
Case Study: Secure C4ISR System Isolation and Data Exchange
Armed Forces Joint Command in the Middle East (GCC)
Extremely high exposure risk due to low-security external sources (UAVs, satellites)
Very high throughput (1 Gbps) with thousands of events per second
Real-time communication requirements, largely based on UDP protocols (e.g. Asterix)
Need for logically bidirectional exchanges within a strictly controlled security model
Highly heterogeneous and legacy systems (UAVs, satellites, radars, SIGINT)
Operation in harsh environments
Need / Problem / Context
Securing Network-Centric Warfare Systems While Enabling Real-Time Command and Control
As part of a transition to network-centric warfare, a defense organization needed to interconnect its C4ISR system with multiple external data sources (UAVs, satellites, radar systems) while maintaining strict isolation of mission-critical systems.
At the same time, the system had to support real-time data ingestion and command transmission to field units, requiring controlled bidirectional logic within a highly constrained and high-risk security environment.
Solution deployed
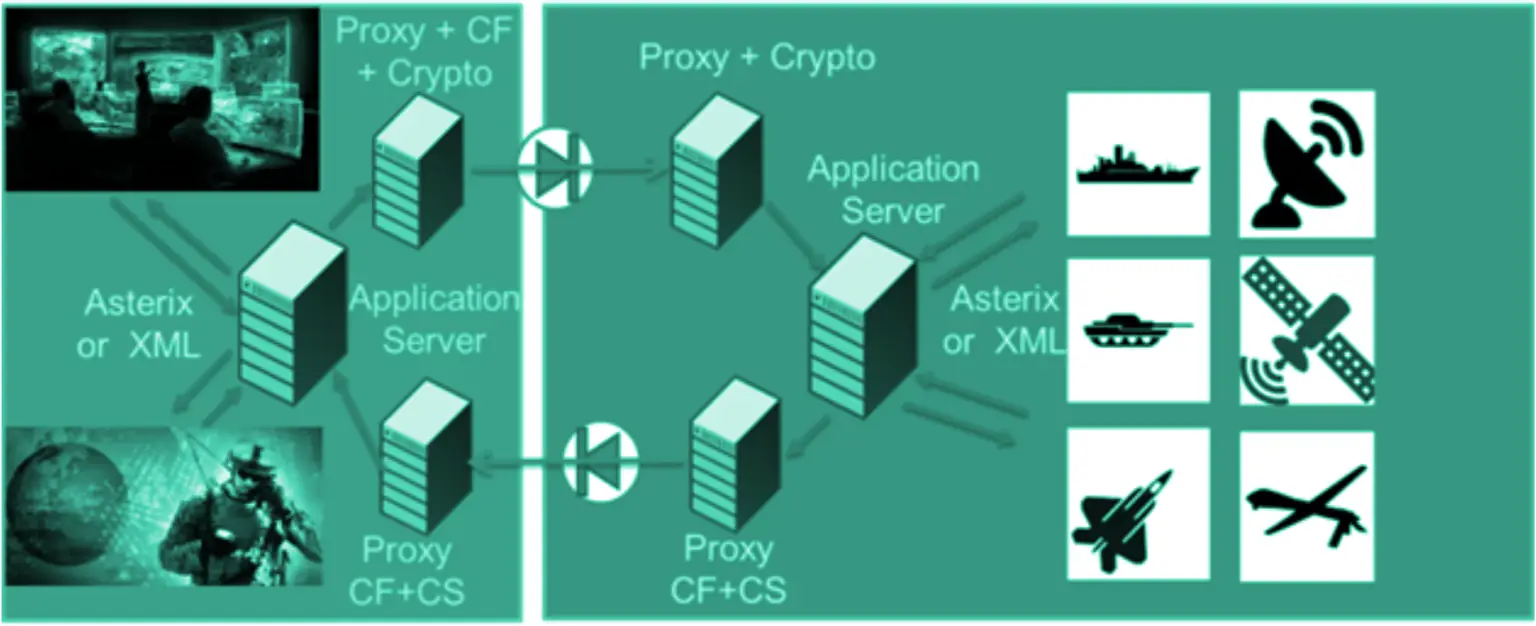
Cyberium implemented a secure cross-domain architecture based on a half-duplex model, enabling controlled asynchronous bidirectional exchanges while preserving strict system isolation. Data flows are physically segmented into independent one-way channels, allowing requests and responses to transit securely without ever establishing a direct bidirectional connection.

13 × OWA 3U @ 1 Gbps
Hardware-enforced unidirectional gateways deployed at scale to segment and secure multiple data flows

NATO-Certified Data Diode
Compliance with defense-grade security requirements for cross-domain data transfe

Filtering and deep packet inspection (DTD/XML)
Fine-grained control and validation of exchanged data structures at the application level

Ruggedized Hardware Option
The system was delivered in a reinforced configuration designed to operate reliably within demanding military infrastructure and operational conditions.
How It Works — Architecture Overview
Outcomes & benefits
Enables secure deployment of C4ISR capabilities with real-time data exchange while maintaining strict protection of mission-critical systems.
Secure C4ISR deployment with protection against state-sponsored cyber threats
Extremely high operational availability (~99.99%) with minimal maintenance
More use cases
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES, SQL Databases Agent
- Gov & Defense
- OWA 2U/3U
- Bitdefender, ClamAV
- SFTP, FTP/S/ES
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES
We secure the Sovereign
— connecting what should stay isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)




