
- Gov & Defense
Case Study: Secure eGates and Visa Data Access
Law Enforcement Agency in the Middle East (GCC)
Extremely high risk due to Internet-exposed destination systems
Real-time or near-zero latency requirements for border control operations
Integration with IBM MQ and asynchronous request patterns
Complex bidirectional logic (request/response) within a constrained security model
Need / Problem / Context
Enabling Secure Real-Time Access to Immigration Data from Untrusted Zones
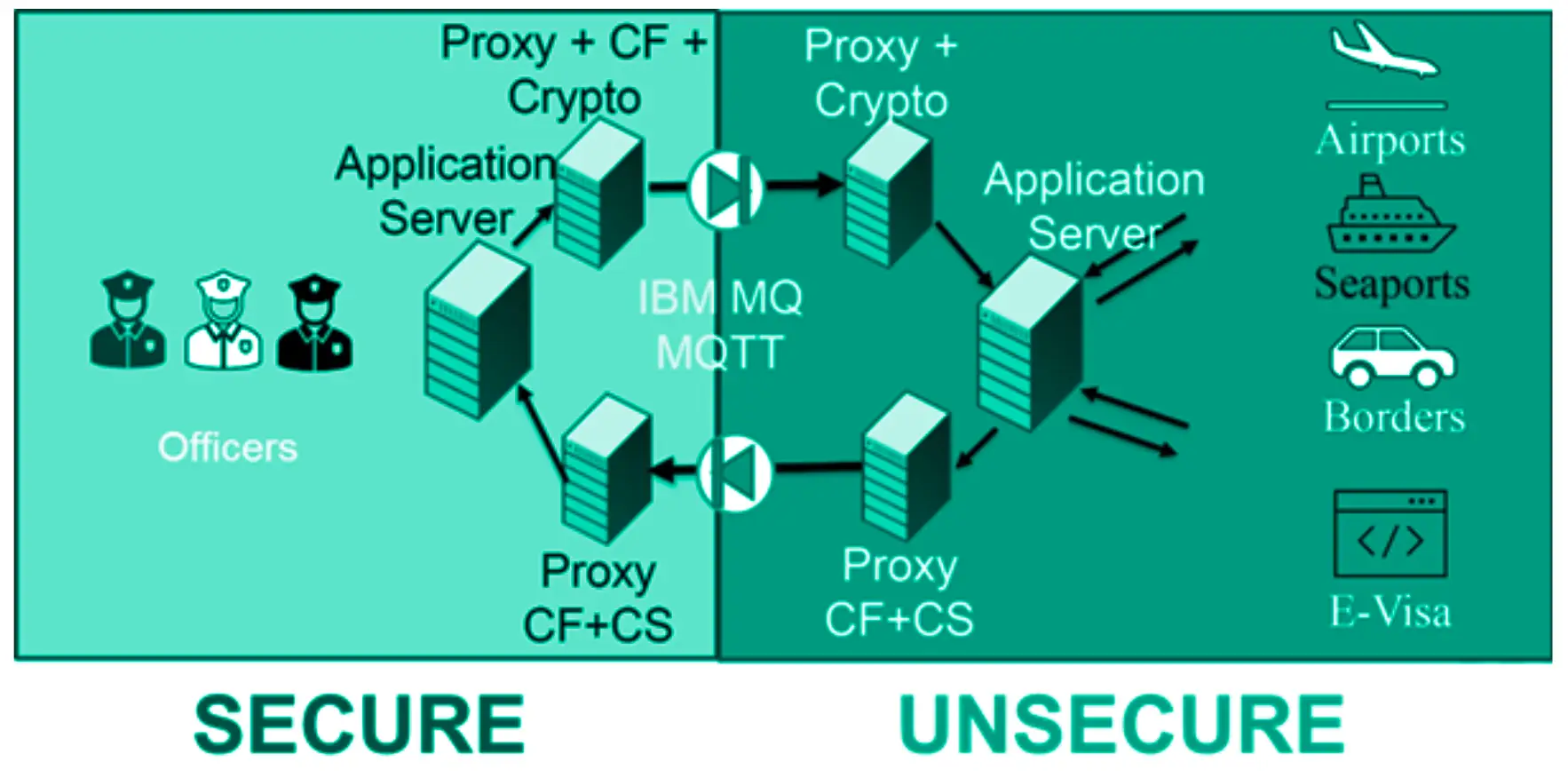
A border control authority needed to provide controlled access to a highly sensitive immigration database from external, non-secure environments, including automated eGates and web-based applications deployed in public-facing zones.
These systems required real-time or near real-time responses to process passenger flows efficiently, while interacting with a core system containing confidential visa and identity data. The challenge was to enable fast and reliable data access for operational use, without exposing the protected environment to any cyber risk, despite the inherently untrusted nature of the requesting systems.
Solution deployed
Cyberium designed a controlled and secure data exchange architecture based on a half-duplex model, combining independent unidirectional flows with advanced application-layer validation mechanisms. This enables asynchronous request/response interactions while ensuring that no direct bidirectional communication path is ever established.

4x OWA 3U @ 1 Gbps
Hardware-enforced unidirectional gateways ensuring secure data transfer across multiple security zones

Filtering and deep packet inspection (DTD/XML)
Fine-grained control and validation of exchanged data structures at the application level

Bespoke Transaction Validation Layer
Includes encryption and digital signature mechanisms to validate each request and response

High-Availability℗ Setup
The architecture incorporates Cyberium patented High Availability mechanisms, ensuring uninterrupted data exchange and eliminating any single point of failure for this mission-critical border control workflow
How It Works — Architecture Overview
Outcomes & benefits
Delivers secure, real-time border operations by enabling fast access to critical data while preserving strict confidentiality and improving overall efficiency.
Secure deployment of automated eGates with controlled access to sensitive immigration data
Significant reduction in passenger waiting times and improved border throughput
Improved data accessibility for officers, enabling better decision-making in real time
More use cases
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES, SQL Databases Agent
- Gov & Defense
- OWA 2U/3U
- Bitdefender, ClamAV
- SFTP, FTP/S/ES
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES
We secure the Sovereign
— connecting what should stay isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)




