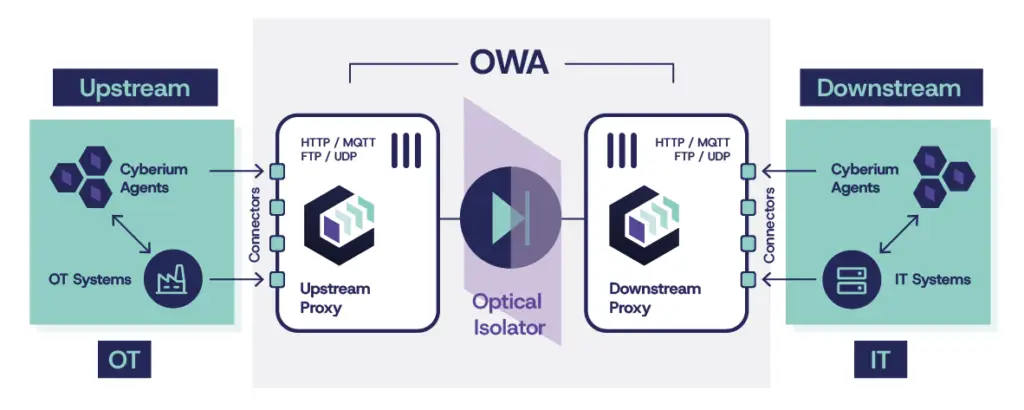
One-Way Appliance
All-purpose hardware-enforced unidirectional network segmentation
Why OWA?
As one of our customers once said, “Because I want to sleep at night.”
Maximum Safety
(One-Way by Design)
- Physically prevents backflow
- Absolute prevention of outsider threats
- Certified European & International security
Real-Time
Operational Efficiency
- Near-zero latency
- Continuity of production
- Optimized for high-availability environments
Reduced
OPEX & CAPEX
- A single appliance drastically reducing control costs
- Very low maintenance
- Lower insurance premiums
Measured end-to-end file transfer performance, including real-world encrypted data flows.
Support for very large files up to 500 GB, with capacity extensible beyond through optional hardware upgrades.
High-frequency transfers exceeding 1,000 files per second for 1 MB payloads, including encrypted data flows, with negligible added latency.
True Layer 1 to 7
Multi-Protocol Break
Breaking protocols, not just packets
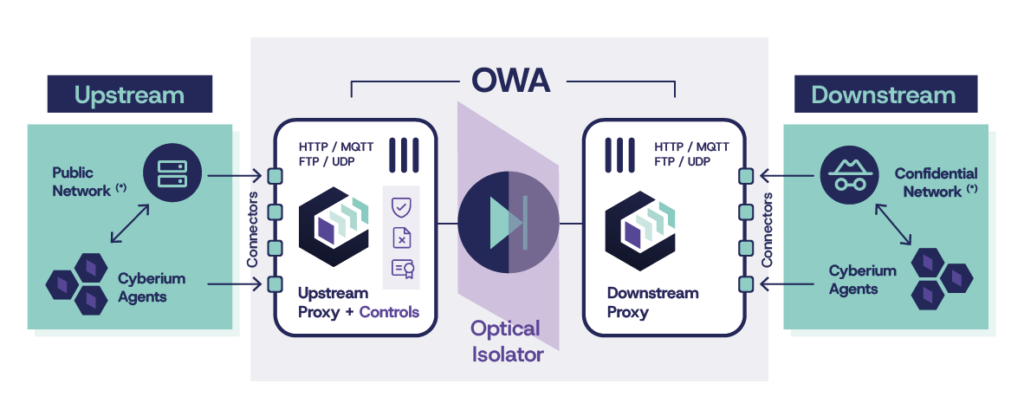
OWA delivers true unidirectional security down to Layer 1, with hardware enforcing one-way isolation across the physical, data link and network layers (L1–L3).
On top of this foundation, intelligent proxy connectors & agents software operates at layers 4–7 to control, adapt and optimize real-world data flows across security domains, seamlessly interleaving and optimizing multi-protocol traffic into a single, efficient optical data stream.

Unmatched Reliability & Resilience
0 packet loss. 0 file corruption. By design.
Error detection and correction by design
OWA embeds integrity verification directly into the transfer process, hashing data to detect any packet loss or modification. Built-in CRC and Forward Error Correction (FEC) mechanisms automatically correct errors, preserving data integrity without requiring acknowledgements or return channels.
Deterministic, loss-free data delivery
OWA guarantees deterministic data transfers across unidirectional links, regardless of throughput, protocol or file size. Protocol-aware handling and controlled transfer mechanisms ensure that every packet and every file reaches its destination intact.
Resilient to downstream network disruptions
OWA integrates downstream buffering and replay mechanisms that preserve data during network degradation or outages. When downstream connectivity is restored, transfers automatically resume — even though the upstream domain, by design, is never informed of the failure.

Patented High Availability℗
Built for uninterrupted operation across critical network boundaries
Achieving true High Availability in a strictly unidirectional environment is inherently complex: no acknowledgements, no control traffic and no upstream visibility into downstream failures.
OWA overcomes these constraints through a patented active-active architecture that maintains continuous data transfer even during downstream outages, component failures or network disruptions.
By combining distributed buffering, automatic failover and autonomous recovery, data flows resume without loss or manual intervention — despite the fundamental limitations imposed by unidirectional communication.
Connectors / Agents Software
An architecture for maximal flexibility and coverage
OWA connectors enable native protocol support while transforming bidirectional communications into secure, hardware-enforced one-way data flows.
Core Replication Features through Replicator Agents
While connectors enable protocol transport, OWA agents provide application-level replication logic on both sides of the diode.
Replication
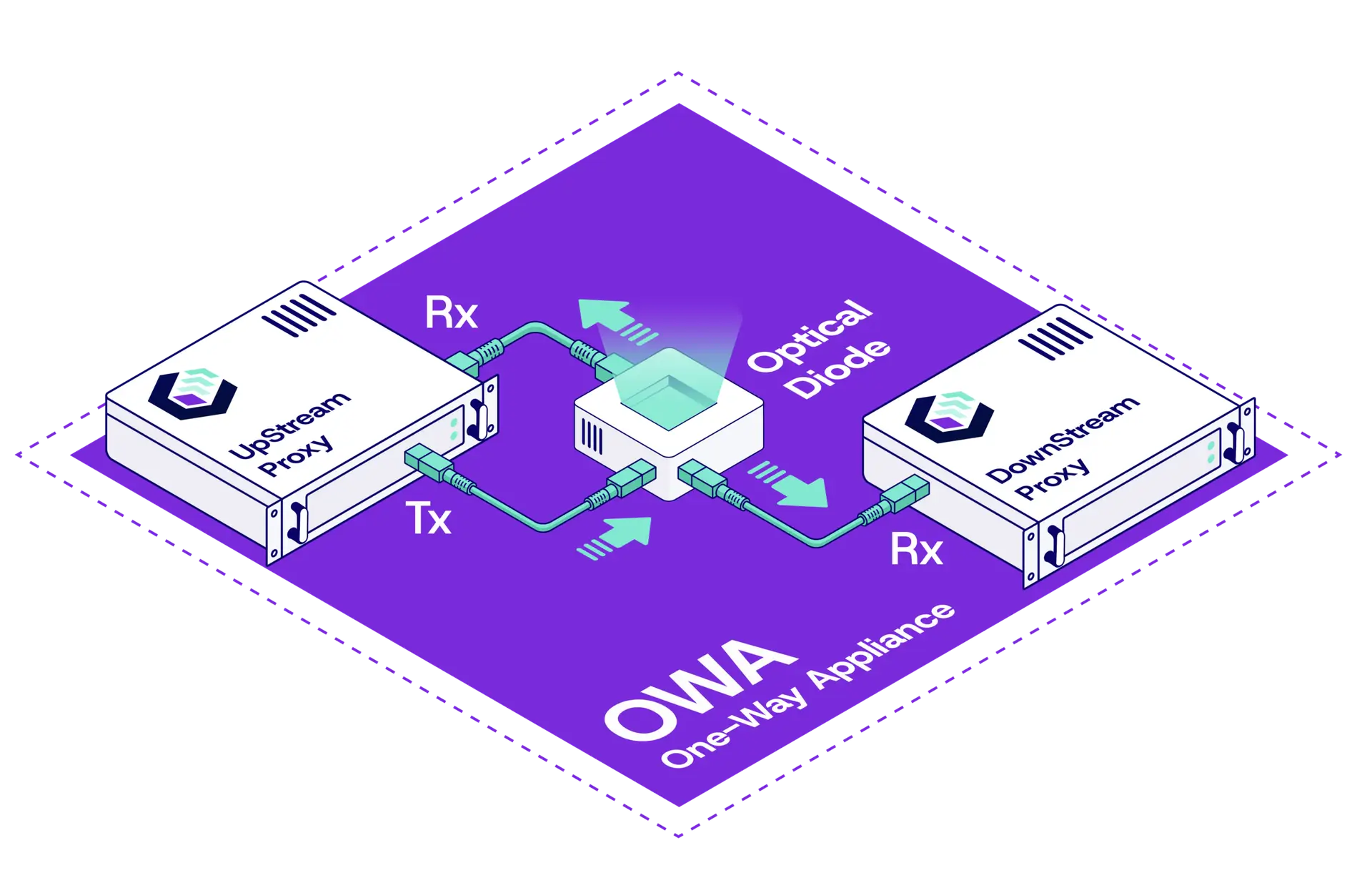
OWA — A Complete Range of Unidirectional Appliances
A modular range combining certified Optical Diode cores with integrated proxy architectures for secure, reliable data transfer.

OWA 1U - 500M/1G
Compact 1U OWA Proxy + Optical Isolator for OT deployments, supporting up to
1 Gbps on selected connectors
Download Datasheet

OWA 2U/3U - 1G
Enterprise-grade OWA Optical Diode + Proxies appliance delivering sustained
1+ Gbps performance with high availability
Download Datasheets

OWA 2U/3U - 10/25G
Extreme-performance OWA Optical Diode + Proxies appliance designed for large-scale data transfers up to 25+ Gbps
Download Datasheet
Model
OWA 1U 500M/1G
OWA 2U/3U 1G
OWA 2U/3U 10/25G
- Form Factor
19” Rack, 1U
19” Rack, 2U + 1U (diode)
19” Rack, 2U + 1U (diode)
- File Transfer
500 Mbps / 1 Gbps in FTPS
True 1+ Gbps
True 10+/25 Gbps
Unidirectional Isolator
Data Diode Options
Data Diode Options
More Details
- Form Factor
19” Rack Mounting, static rails
1U Rack Space for the two proxies
physically separated (½ U each)
19” Rack Mounting, sliding rails. 2U Rack Space for the two proxies + 1U for the Optical Diode option
19” Rack Mounting, sliding rails. 2U Rack Space for the two proxies + 1U for the Optical Diode option
- Dimensions & Weight
W 479 x D 420 x H 44 (total)
12 Kg / 26,5 Lb (total)
W 482 x D 548 x H 43 (per proxy)
13,2 Kg / 29,2 Lb (per proxy)
W 482 x D 817 x H 43 (per proxy)
17,5 Kg / 38,6 Lb (per proxy)
- Power Supply
2x 400 W PSU
4 x 600 W PSU
(2 per 1U proxy)
4 x 800 W PSU
(2 per 1U proxy)
- File Transfer Capacities
Above 1000 files of 64 KB sent /sec at 500 Mbps in FTPS
Above 1000 files of 125 KB /sec. Max file size 100 GB. Possible hardware upgrade
Above 1000 files of 1 MB /sec. Max file size 500 GB. Possible hardware upgrade
Limited to 2 concurrent connectors
Off-Proxy Software Agents
Unlimited concurrent connectors
On/Off-Proxy Software Agents
Unlimited concurrent connectors
On/Off-Proxy Software Agents
- High Availability
On Roadmap
Active-active HA with automatic failover ℗
Unidirectional Optical Link/Isolator
Unidirectional Optical Link/Isolator or choice amongst 3 optional Optical Diodes
Unidirectional Optical Link/Isolator or choice amongst 3 optional Optical Diodes
- Reverse Mode, Antivirus and Filtering
Not Included
Reverse-mode e.g. IT-to-OT or Public-to-Restricted supported with Dual Antivirus option
File-filtering based on true file type detection and JSON/XML content inspection (Option)
Reverse-mode e.g. IT-to-OT or Public-to-Restricted supported with Dual Antivirus option
File-filtering based on true file type detection and JSON/XML content inspection (Option)
Form Factor / Power Supply / Dimensions & Weight
OWA-1U-500M-1G
19” Rack Mounting, static rails 1U Rack Space for the two proxies physically separated (½ U each)
2x 400 W PSU
W 479 x D 420 x H 44 (total) | 12 Kg / 26,5 Lb (total)
OWA-3U-1G
19” Rack Mounting, sliding rails. 2U Rack Space for the two proxies + 1U for the Optical Diode option
4 x 600 W PSU (2 per 1U proxy)
W 482 x D 548 x H 43 (per proxy) | 13,2 Kg / 29,2 Lb (per proxy)
OWA-3U-10G-25G
19” Rack Mounting, sliding rails. 2U Rack Space for the two proxies + 1U for the Optical Diode option
4 x 800 W PSU (2 per 1U proxy)
W 482 x D 817 x H 43 (per proxy) | 17,5 Kg / 38,6 Lb (per proxy)
Performance / Capacities
OWA-1U-500M-1G
Above 1000 files of 64 KB sent /sec at 500 Mbps in FTPS.
Limited to 2 concurrent connectors & Off-Proxy Software Agents
High Availability On Roadmap
OWA-3U-1G
Above 1000 files of 125 KB /sec. Max file size 100 GB. Possible hardware upgrade.
Unlimited concurrent connectors & On/Off-Proxy Software Agents
Active-Active High Availability with automatic failover℗
OWA-3U-10G-25G
Above 1000 files of 1 MB /sec. Max file size 500 GB. Possible hardware upgrade.
Unlimited concurrent connectors & On/Off-Proxy Software Agents
High Availability Not Available
Security
OWA-1U-500M-1G
Unidirectional Optical Link/Isolator
Advanced Security Features not included
OWA-3U-1G
Unidirectional Optical Link/Isolator or choice amongst 3 optional Optical Diodes
ANSSI (FR) – NATO – EAL7+
Reverse-mode e.g. IT-to-OT or Public-to-Restricted supported with Dual Antivirus option
File-filtering based on true file type detection and JSON/XML content inspection (Option)
OWA-3U-10G-25G
Unidirectional Optical Link/Isolator or choice amongst 3 optional Optical Diodes
ANSSI (FR) – NATO – EAL7+
Reverse-mode e.g. IT-to-OT or Public-to-Restricted supported with Dual Antivirus option
File-filtering based on true file type detection and JSON/XML content inspection (Option)
Compatible Diode Certifications
Certifications apply to optional OEM diode components integrated at the core of OWA, fully tested and validated to ensure independently evaluated, hardware-enforced unidirectional security.
ANSSI Certified Optical Core
OWA can be configured around an optical core technology qualified by ANSSI, the French National Cybersecurity Agency. This configuration integrates the Allentis Tapics passive optical diode, recognized for high-assurance sovereign deployments.
The ANSSI qualification validates the physical unidirectional enforcement mechanism at hardware level under a formal national evaluation scheme. This ensures that the security boundary itself — the optical isolation core — is independently assessed and approved by a recognized sovereign authority.



NATO / EU Secret Optical Core
OWA can be configured with an optical core designed to meet NATO Secret and EU Secret deployment requirements, ensuring suitability for classified cross-domain environments.
In this configuration, OWA integrates the Thales ELIPS SD passive optical diode, qualified by ANSSI and evaluated at assurance levels equivalent to EAL7+ under national schemes. Engineered for defense-grade data exchange under stringent governmental security frameworks, its unidirectional enforcement mechanism supports the secure transfer of sensitive information while preserving strict domain separation for sovereign and high-impact infrastructures.



Common Criteria Evaluation - EAL 7+
OWA can be configured with an electro-optical core evaluated up to Common Criteria EAL7+, representing the highest formal assurance levels achievable for a security enforcement component.
In this configuration, OWA integrates the Sentyron Ruggedized (1G / 10G) electro-optical diode, whose unidirectional enforcement mechanism has undergone formal design verification and advanced vulnerability analysis. This level of evaluation is particularly suited for defense, classified and high-consequence critical infrastructure environments where architectural trust must rely on mathematically verified security properties.


Industrial Security Frameworks (ISA-IEC 62443)
Beyond component-level certification, OWA architectures are designed to support compliance with major industrial and governmental frameworks such as IEC/ISA-62443, NIS2, and national critical infrastructure regulations.
By enforcing hardware-level one-way communication and structurally reducing inbound attack surfaces, OWA simplifies security proofs, eases audits, and reduces the number of compensating controls required to achieve higher security levels (e.g., SL3–SL4). This structural approach also supports stronger cybersecurity insurance positioning and risk assessment outcomes.




As a Sovereign Diode Vendor, why should I partner with Cyberium and request a Compatibility Evaluation?
Focus your sovereignty efforts on the critical hardware security layer while our proxies handle non-critical, yet highly complex application functions (for which R&D costs are leveraged accross numerous deployments) — enabling more reliable, faster and full-feature multi-protocol data exchange.

Cross-Domain Solution (CDS)
OWA evolves from one-way gateway to fully integrated cross-domain security
OWA extends hardware-enforced unidirectional security with integrated cross-domain protection mechanisms, enabling complex, asynchronous bidirectional workflows across multiple security domains, always relying on a strict unidirectional hardware Data Diode at its core — ensuring that data exchanged between environments remains safe, compliant and operationally usable, even in high-risk or reverse-flow scenarios, from public or less-secure zones to the most sensitive and classified environments.
Dual antivirus deep file inspection
Ensure malware-free data transfer with high-performance, wire-speed scanning engines


Deep Content Disarm and Reconstruction (CDR)
Sanitize and rebuild files by removing all active or potentially malicious content, ensuring only safe, usable data is transferred across domains.
Unlike detection-based approaches, CDR assumes all files are untrusted and reconstructs them into clean, compliant versions — protecting against zero-day and evasive file-based threats.
Asynchronous bidirectional data workflows
Enable secure data exchange using dual diodes for controlled, two-way transfers
Granular content filtering and validation
Enforce strict control using true file type detection and structured data inspection
Custom processing and validation workflows
Implement automated and human-driven controls for secure, auditable data exchanges
Trusted Across Critical Sectors
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA, Siemens WinCC
- SQL Databases Agent
- Critical OT & Industry 4.0
- OWA 2U/3U
- GE OSM (On-Site Manager)
- File Transfer Agent, SFTP, FTP/S/ES
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA
- SQL Databases Agent
- Gov & Defense
- OWA 2U/3U
- Bitdefender, ClamAV
- SFTP, FTP/S/ES
Quietly Appreciated by Sovereign Entities Worldwide

We installed a pair of Cyberium Data Diodes and proxies on an offshore rig in 2015. Eleven years later, they are still running continuously without a single on-site maintenance intervention. At some point, I honestly forgot about them… until I realized they were still there, quietly doing their job.
(abr: different brand/company name at the time, but same product making)
Offshore Operations Director, Top-5 Global Oil & Gas Company
Our Cyberium Data Diode has been running 24/7 for seven years now without a single file dropped or corrupted. In our environment, we simply cannot afford data loss. After seven years, it has never given us a reason to worry.
(abr: different brand/company name at the time, but same product making)
Engineering Manager, E-Gate Border Control Systems - Middle East
We were running eight diodes before. It was complicated and, frankly, fragile. With Cyberium, we moved to a single device. It simplified the architecture overnight. Now it’s predictable, easier to monitor, and we’re not constantly dealing with small operational issues.
Lieutenant M., Cybersecurity Division - National Security Agency (Middle East)
Why do I insist on deploying Cyberium Data Diodes on every OT/IT connection without exception? Because I want to sleep peacefully.
Senior System Engineer, Major Gas Operator (Middle East)
In my opinion, the deployment significantly increased our confidence in the security of our OT network, while still allowing us to provide data to the Corporate network.
Senior Industrial OT Department Leader, National Electricity Grid (ASEAN)
We secure the critical
— connecting what should stay isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)