Unidirectional Network Segmentation Gateway
Enabling OT data-driven digital transformation, Big Data and AI,
while natively complying with the most stringent cyber security standards.
“If you are critical enough to be a target, expect state-level capabilities against your defenses"
Industrial environments are undergoing a profound transformation: OT data now drives performance, safety and digital innovation — while increased connectivity exposes control systems to cyber threats with real-world physical consequences.
In a context where adversaries increasingly seek disruption rather than ransom, the convergence of IT and OT reshapes risk assumptions, making production continuity, safety and infrastructure resilience strategic concerns. Cybersecurity can no longer rely primarily on detection and remediation, and must shift toward prevention and structural protection.
Key Cybersecurity Challenges to Overcome
Critical OT Infrastructure Risk Landscape — In Numbers
Digital convergence is reshaping industrial risk, expanding exposure across critical OT infrastructures.
Increase in security incidents targeting critical infrastructure since 2022
of OT attacks originate from initial IT breaches
of industrial organizations say IT/OT convergence is key to achieving their business goals
Why Cyberium’s Solution is a Natural Fit for Securing Critical Infrastructures?
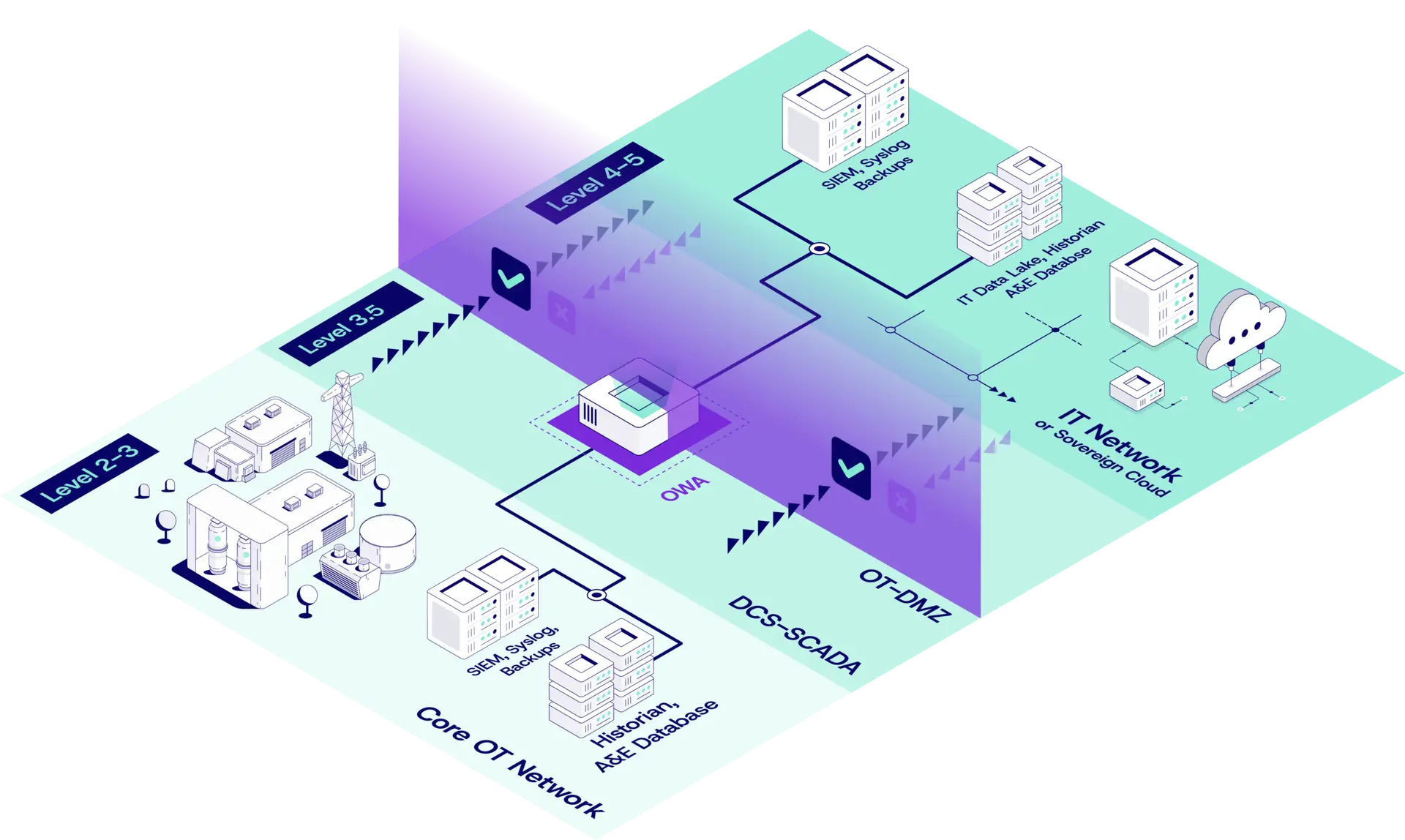
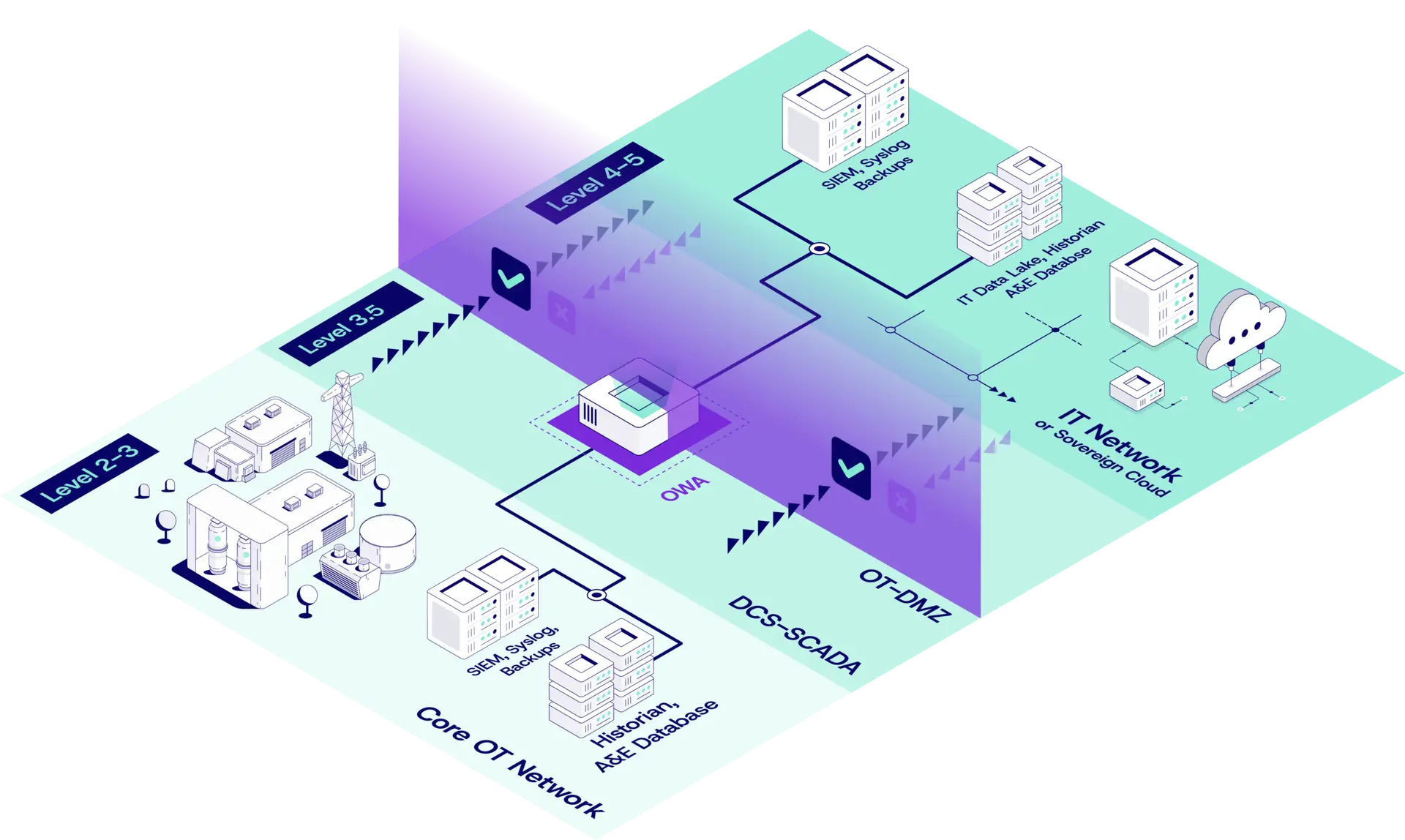
Unidirectional Hardware Segmentation that Stops Remote APTs by Design
Physical segmentation aligned with the highest IEC/ISA-62443 security objectives
In critical OT environments, advanced threats primarily exploit bidirectional connectivity, software vulnerabilities and configuration errors. Firewall-based segmentation relies on layered, software-defined controls and continuous maintenance, requiring multiple compensating measures to reach higher security levels.
By enforcing strict unidirectional network segmentation in hardware, Cyberium eliminates inbound communication paths by design. This intrinsic reduction of the attack surface provides deterministic protection against remote APTs and directly supports IEC/ISA-62443 security objectives up to SL3–SL4, without relying on complex rule sets or ongoing compensating controls.
Guaranteed OT Data Uplift without Expanding the Attack Surface
Supporting IT/OT convergence without inheriting IT risk
Industrial performance, monitoring and compliance increasingly depend on OT data flowing to IT, SOC or analytics platforms. The challenge is enabling this data uplift without inheriting IT-side exposure.
Cyberium provides a complete OT-to-IT enablement stack, combining protocol-aware replication and best-of-breed connectors across historians and SCADA, alarms and events, SIEM platforms and industrial data services. From time-series and RTU data to OPC UA, Syslog, SFTP/FTPS, MQTT or industrial protocols, OT data becomes directly usable upstream for predictive maintenance, centralized monitoring and compliance — without redesigning existing OT architectures or toolchains.
Designed for Long-Lifecycle, Safety-Critical Industrial Operations
Operational flexibility, trusted integration
OT environments run continuously, often for decades, under strict safety and availability constraints. Security mechanisms that introduce downtime, frequent updates or fragile dependencies are incompatible with these realities.
Cyberium’s network segmentation is built on enterprise-grade, mission-critical hardware designed for uninterrupted operation, integrating seamlessly into existing OT architectures while preserving availability, safety and operational continuity — even under failure or maintenance conditions
Integrated with Major Industrial Ecosystems
Validated, embedded or referenced within selected OEM Cybersecurity Solutions






Industry-Specific Applications
Multiple verticals, one shared OT security reality: safety, compliance and connectivity.
Electricity — Grid and Generation Resilience
Modern power systems are integrating smart grid technologies to optimize generation, distribution, and demand response. However, increased connectivity, automation and data exchange expands the attack surface, exposing substations, control systems and field devices to cyber threats that can cause cascading service outages or unsafe states. OT security must balance availability, safety regulation and evolving cyber threats, including state-sponsored attacks with physical impact.
NIS2 and similar frameworks emphasize risk management across IT and OT — requiring robust segmentation to protect SCADA and distribution control networks without impairing operational continuity.
Segment SCADA and substation control domains from enterprise IT to limit lateral movement.
Secure remote telemetry and command links within distribution networks while preserving regulatory compliance.

Oil & Gas — Protecting Production, Distribution and Safety Systems
Oil & gas facilities combine complex OT stacks (SCADA, PLCs, ICPS) with remote and offshore operations that rely on automated control and sensor networks. As digital transformation connects previously isolated assets, cyber threats can affect not only production continuity but also worker safety and environmental integrity. Offshore and subsea systems face heightened OT risk due to hybrid IT/OT controls and constrained maintenance windows, often with limited ability to patch or update.
Secure remote control paths for offshore platforms, ensuring critical commands cannot be forged or tampered with.
Protect pipeline control systems against IT-driven lateral attacks while enabling safe telemetry to central operations.

Water Treatment — Safeguarding Public Safety and Compliance
Water treatment plants depend on OT systems to manage pumps, valves and chemical dosing that directly affect public health. OT cybersecurity here must prevent unauthorized interference with treatment processes, maintain compliance under regulations like NIS2, and support reporting to regulators — all without compromising service availability. Integration with IT and analytics drives operational efficiency but also introduces risks of malicious manipulation or unintended control loops. Ensuring proper segmentation and supervised data flows is vital to prevent data corruption or process disruption.
Isolate critical physical control loops from administrative networks and external access.
Enable secure supervisory data feeds to analytics and compliance platforms.

Transportation — Securing Mobility and Control Systems
Transportation systems (rail, metro, airports) rely on OT to manage signaling, vehicle control, and infrastructure operations. Cyber risks in these environments can lead to service disruption, safety hazards, and widespread operational impacts — especially when IT networks are connected to OT for scheduling, monitoring or reporting. Critical transportation systems increasingly fall under NIS2 or similar directives, demanding structured OT risk management, segmentation and assurance.
Segment signaling and control systems from ticketing and enterprise networks.
Protect remote diagnostics and location data feeds without exposing control channels.

Chemicals — Process Safety and Cyber Risk Integration
Chemical production plants operate highly sensitive processes where cyberattacks on OT can result in dangerous reactions, leaks or contamination. These environments often use legacy equipment with limited built-in security, making segmentation and risk isolation critical. OT security in chemical production must be tightly integrated with industrial safety management and regulatory compliance frameworks, prioritizing both cybersecurity and process safety assessments (e.g., cyber PHA / cyber HAZOP).
Ensure integrity of control loops for reactors and hazardous substance handling.
Enable secure data sharing with MES/ERP systems for quality control and compliance reporting

Hospitals & Health — Protecting Medical CDS and Operational Systems
Healthcare facilities rely on OT systems for building management, medical equipment control and life-critical systems. Cyber intrusions can compromise patient safety or disrupt critical care delivery. With healthcare providers now classified under expanded critical infrastructure scopes like NIS2 and ENISA guidelines, OT systems in hospitals must be segmented to prevent lateral movement from enterprise IT, and data flows must be secured to support reliability, privacy and regulatory reporting.
Segment medical device networks and building automation systems from administrative IT
Secure operational telemetry and alarms to SOCs for compliance and incident monitoring

Trusted Across Critical Sectors
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA, Siemens WinCC
- SQL Databases Agent
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA
- OPC UA Agent
- Critical OT & Industry 4.0
- OWA 2U/3U
- Cisco Splunk
- HTTP/S API, Syslog
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA
- SQL Databases Agent
- Critical OT & Industry 4.0
- OWA 2U/3U
- Hexagon PAS
- File Transfer Agent, SMTP
- Critical OT & Industry 4.0
- OWA 2U/3U
- GE OSM (On-Site Manager)
- File Transfer Agent, SFTP, FTP/S/ES
Key Benefits. With Cyberium, Gone are the Days of...
Zero-day Panic
Rush-patching eliminated by removing inbound attack paths
Frustrating Air-gap
Air-gap riturals replaced by automated data flows
Move beyond reactive cybersecurity. Protect your perimeter while delivering measurable ROI.
Fewer controls to implement for compliance, simplified audits and cybersecurity proofs, lower maintenance effort in restricted OT zones — and reduced cyber insurance premiums driven by lower structural risk.
Soaring OPEX
Killed by near-zero security maintenance and reduced unplanned downtime
Endless Updates
Avoided, allowing teams to refocus on system control and operations
Protected by our solution for Critical OT & Industry 4.0








We secure the critical
— connecting what should stay isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)




