- Critical OT & Industry 4.0
- Custom SCADA, Siemens WinCC
Case Study: Enabling global balancing & monitoring across Siemens WinCC-based Water Treatment sites
Water Treatment Plant in the Middle East (GCC)
Continuous SCADA data flows from RTUs to central IT systems
Vulnerable legacy environments without authentication or encryption
High exposure to ransomware and Advanced Threat Actors
Need / Problem / Context
Centralized Water Network Optimization Under Cyber Constraints
A major water treatment operator in the GCC relies on a centralized IT control center to monitor and optimize multiple distributed treatment stations running Siemens WinCC SCADA systems. This architecture enables global balancing of water production and efficient operations across regions.
To support this, SCADA data from local RTUs must be continuously exposed to IT systems. However, these environments are based on highly vulnerable legacy systems, lacking authentication and encryption, and cannot be modified without operational risk.
At the same time, the operator faces increasing threats from ransomware and Advanced Threat Actors targeting industrial infrastructures. The challenge was therefore to enable centralized monitoring and optimization while ensuring strict protection of RTUs — without impacting or modifying legacy Siemens WinCC environments.
Solution Deployed
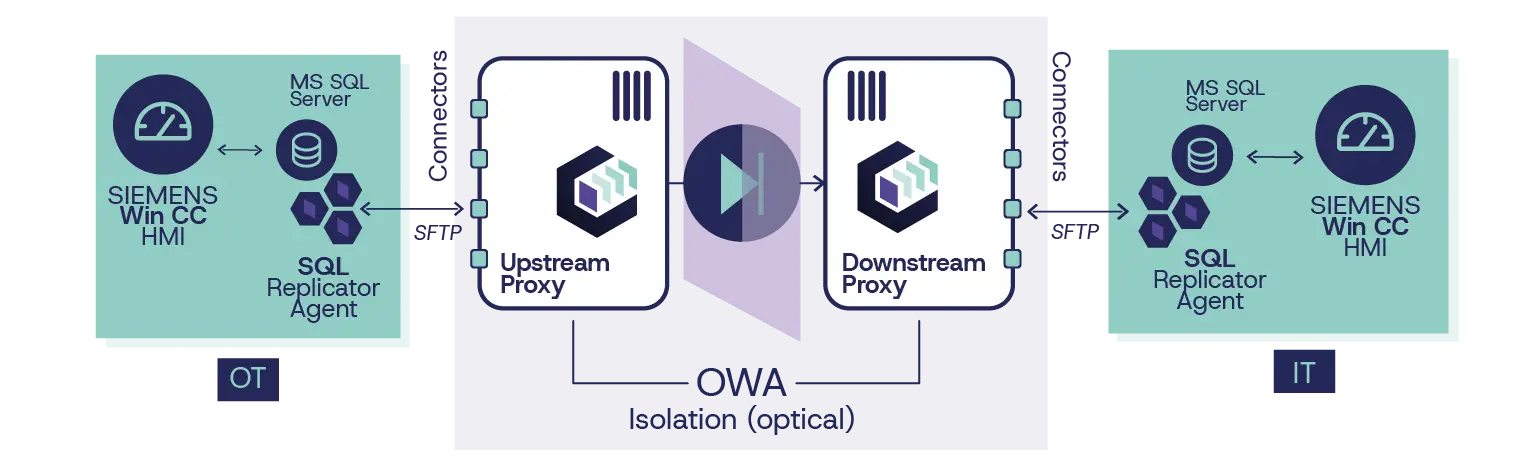
Cyberium deployed a unidirectional architecture enabling secure WinCC SCADA database replication from OT to IT, without any inbound connectivity. The solution combined OWA appliances with SQL replication agent and secure file transfer mechanisms, ensuring seamless data synchronization while preserving strict isolation of legacy systems.

2x OWA 3U pack @ 1 Gbps
Two security gateways (one by physical site) were deployed to sustain continuous high-volume scada replication while preserving strict separation between OT and IT environments.

Real Time MS SQL Replicator Agent
A database-aware replication component that detects MS SQL changes in real time and replicates them granularly across the diode — ensuring continuous synchronization while preserving data integrity, structure and consistency for IT systems.

Standard (SFTP) Connector
A reliable file-based transfer mechanism underpinning the MS SQL Replicator Agent, ensuring secure, high-integrity data exchange across the unidirectional link, with built-in robustness for continuous and lossless delivery.
Outcomes & benefits
Enabled centralized monitoring and optimization of water operations, with absolute OT protection
Delivered real-time SCADA data to IT, enabling global operational decision-making
Improved resource allocation and balancing across distributed treatment sites
Secured legacy RTU environments without modification or operational disruption
Eliminated all IT-to-OT attack paths, protecting critical water infrastructure
More use cases
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA, Siemens WinCC
- SQL Databases Agent
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA
- OPC UA Agent
- Critical OT & Industry 4.0
- OWA 2U/3U
- Cisco Splunk
- HTTP/S API, Syslog
- Critical OT & Industry 4.0
- OWA 2U/3U
- Custom SCADA
- SQL Databases Agent
- Critical OT & Industry 4.0
- OWA 2U/3U
- Hexagon PAS
- File Transfer Agent, SMTP
- Critical OT & Industry 4.0
- OWA 2U/3U
- GE OSM (On-Site Manager)
- File Transfer Agent, SFTP, FTP/S/ES
We secure the Critical
— connecting what should isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)