
- Gov & Defense
Case Study: Secure Watchlist Distribution for Border Control
Law Enforcement Agency in the Middle East (GCC)
Extremely high exposure risk due to Internet-facing destination systems
Full database replication of a MS SQL Server Enterprise environment
Requirement for continuous availability and consistency of watchlist data
Need for secure high-availability architecture
Need / Problem / Context
Securing Real-Time Watchlist Access at Airport Borders
A government law enforcement agency needed to securely distribute a sensitive national watchlist database to an external application used at airport border control checkpoints. This application, partially exposed to the Internet, required continuous access to up-to-date data to support real-time identity verification and threat detection.
The challenge was to enable seamless and reliable data availability at the operational edge, while ensuring that the classified source environment remained fully isolated and protected from any potential cyber intrusion or backflow risk.
Solution deployed
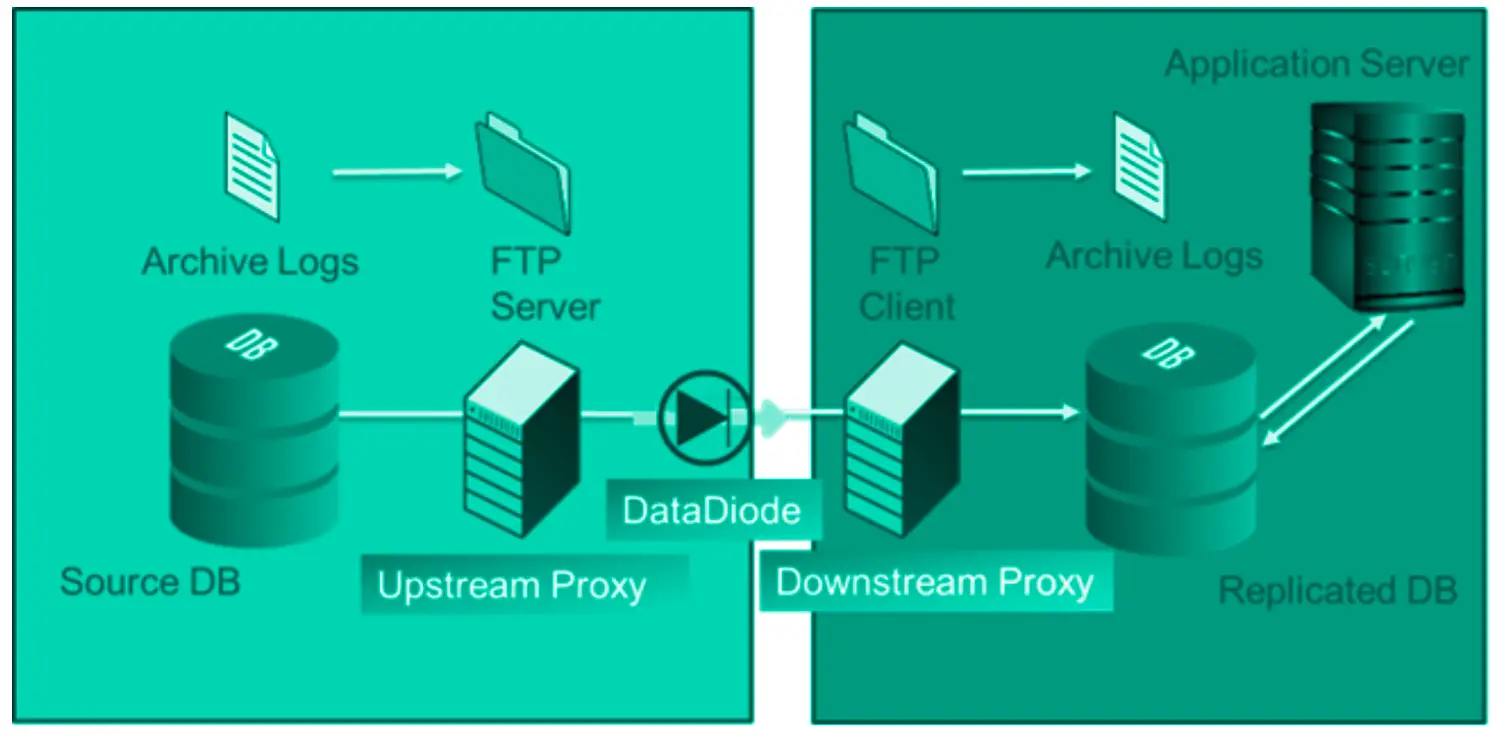
Cyberium implemented a resilient unidirectional replication architecture designed to ensure secure and continuous database distribution without exposing the source environment.

2x OWA 3U @ 1 Gbps
Hardware-enforced unidirectional gateway ensuring secure, one-way data transfer from the classified environment
MS SQL Differential Backup Agent
Enables efficient incremental database replication without direct database exposure

Standard Connector (SFTP)
Standard connector enabling structured and controlled file ingestion across domains

High-Availability℗ Setup
The architecture incorporates Cyberium patented High Availability mechanisms, ensuring uninterrupted data replication and eliminating any single point of failure for this critical operational data flow.
How It Works — Architecture Overview
Outcomes & benefits
The solution enabled secure operational use of sensitive data at scale while maintaining strict network isolation.
Real-time watchlist availability at checkpoints, enabling live identification of high-profile individuals
Zero cybersecurity incidents since 2018 despite serving over 100 million users annually
Continuous data availability with no compromise of the classified environment
More use cases
- Gov & Defense
- OWA 2U/3U
- Bitdefender, ClamAV
- SFTP, FTP/S/ES
- Gov & Defense
- OWA 2U/3U
- SFTP, FTP/S/ES
We secure the Sovereign
— connecting what should stay isolated.
Latest blog entries
- AI & Cybersecurity, Threat Landscape
In 2025, the baseline assumption of industrial cybersecurity broke. For twenty years, defenders had one reliable edge over attackers: time. (…)
- OT Cybersecurity Best Practices, Threat Landscape
Every documented OT breach in the past five years started at the same place: an internet-facing asset that operators believed (…)
- OT Cybersecurity Best Practices, Regulations & Compliance, Threat Landscape
In every major OT cyberattack of the past decade, firewalls were present. In each case, they failed. Not because they (…)
- Architecture Design Patterns, Engineering Insights
Industrial cybersecurity starts with a simple reality: you cannot detect threats if you cannot see what happens inside your OT (…)




